USN-2930-1: Linux Kernel vulnerabilities. Canonical releases major Kernel update and patches seven Linux Kernel vulnerabilities in Ubuntu 15.10. Update Ubuntu now.
Ubuntu Security Notice USN-2930-1
- The Linux netfilter implementation did not correctly perform validation when handling IPT_SO_SET_REPLACE events. A local unprivileged attacker could use this to cause a denial of service (system crash) or possibly execute arbitrary code with administrative privileges. (CVE-2016-3134)
- An integer overflow in the Linux netfilter implementation. On systems running 32 bit kernels, a local unprivileged attacker could use this to cause a denial of service (system crash) or possibly execute arbitrary code with administrative privileges. (CVE-2016-3135)
- The USB driver for Clie devices in the Linux kernel did not properly sanity check the endpoints reported by the device. An attacker with physical access could cause a denial of service (system crash). (CVE-2015-7566)
- A condition existed when handling heartbeat- timeout events in the SCTP implementation of the Linux kernel. A remote attacker could use this to cause a denial of service. (CVE-2015-8767)
- A condition existed in the ioctl handler for the TTY driver in the Linux kernel. A local attacker could use this to cause a denial of service (system crash) or expose sensitive information. (CVE-2016-0723)
- The ALSA USB MIDI driver incorrectly performed a double-free. A local attacker with physical access could use this to cause a denial of service (system crash) or possibly execute arbitrary code with administrative privileges. (CVE-2016-2384)
- The USB driver for Treo devices in the Linux kernel did not properly sanity check the endpoints reported by the device. An attacker with physical access could cause a denial of service (system crash). (CVE-2016-2782)
Update instructions
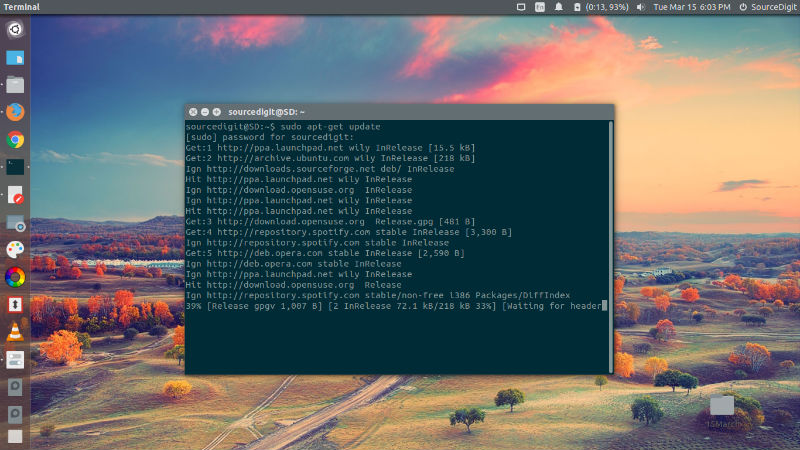
To update your system, please run the following commands:
sudo apt-get update
sudo apt-get upgrade
After system updates, please reboot the system to make all the necessary changes.
